Update: instead of saying “not enough data” search console incorrectly says “failing”. They are fixing this bug report in Search Console. If your site is properly on https, then there’s nothing you need to do.
The new Page experience on mobile report in Google Search Console is showing insufficient HTTPS coverage on your site, and yet, my website is using SSL for all the URLs? So what is going on?
How to Fix Insufficient HTTPS Coverage on Your Site
Here’s the Checklist for Fixing Insufficient HTTPS coverage on your site as shown in the above video lesson.
Server Configuration
Insights contained herein assumes that you are familiar with editing website files. And that you have web hosting services with cPanel access. Most websites today can check server redirection rules and particularly any 301 directives found in server configuration files such as .htaccess
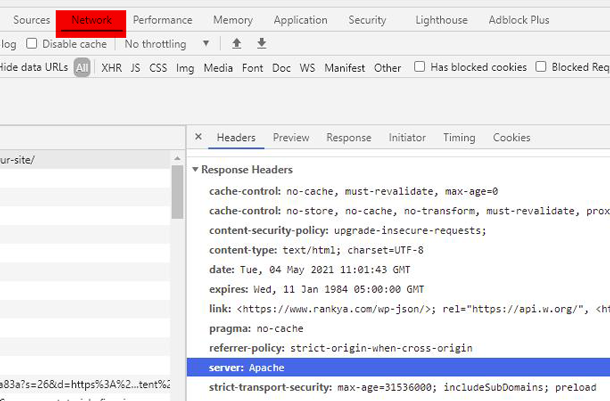
Furthermore: web technologies are diverse, your website may be using Apache, NGINX, IIS, CDN or others such as Cloudflare. That means there are many different configuration settings, first step is to identify the type of server your website is setup using.
Simple way to check is to use a web browser (Chrome, FireFox, Internet Explorer) web dev toolbar. Access this mode pressing the F12 key on your keyboard. Then, go to the “Network” tab and find Response Headers as shown in the below image
If you know that your website is thoroughly meeting Google Webmaster Guidelines. Then follow these steps. Your web hosting service provider help section will show you which .htaccess rules will work for your website. Because there are many different directives which accomplishes the same outcome. Here are some samples rules to test. Below codes are for web servers built on Apache server, but you can still gain an insight for using .htaccess rules.
Here’s an Insight That Will Help Fixing HTTPS Failing Issues in GSC
Domain Name System (DNS) when requesting a website address such as https://www.example.com/ doesn’t actually call that address, but rather call example.com. That means, the 4 amigos
- http
- https
- www
- non-www
Using any of the above format when requesting a website will resolve DNS to show a website. Meaning, Googlebot first requests the top-level domain (TLD) which is the highest level in the hierarchical Domain Name System. HTTPS may be failing if Googlebot requesting your TLD address example.com encounters NON-SSL version along the redirection chain.
Since there are so many different scenarios which may be causing this issue in Search Console, below, I’ve grouped various different solutions you can test to resolve this problem. For most setups, its usually the web server .htaccess file directives that can solve the insufficient HTTPS Coverage problems making sure that 4 amigos are only serving 1 address (the one you are using on your website).
IMPORTANT
When using .htaccess file rules for apache software, most servers will require redirection rules to be within IfModule mod_rewrite.c and also have RewriteEngine capabilities turned on
<IfModule mod_rewrite.c>
RewriteEngine On
#your redirection rules goes here
</IfModule>
Remember, if you test any rules here and it doesn’t work, then try including Options +FollowSymLinks and re-test your directives
<IfModule mod_rewrite.c>
Options +FollowSymLinks
RewriteEngine On
#your redirection rules goes here
</IfModule>
Redirect Visitors to SSL Secured Version of a Site Example 1 (NON-WWW)
RewriteEngine on
RewriteCond %{HTTPS} off
RewriteRule (.*) https://example.com/$1 [R=301,L]
Redirect Visitors to SSL Secured Version of a Site Example 1a (WWW)
RewriteEngine on
RewriteCond %{HTTPS} off
RewriteRule (.*) https://www.example.com/$1 [R=301,L]
Redirect Visitors to SSL Secured Version of a Site Example 2
This particular code will use IfModule mod_rewrite directing all version of http & https using ENV:PROTO
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteCond %{HTTPS} =on
RewriteRule ^ - [E=PROTO:https]
RewriteCond %{HTTPS} !=on
RewriteRule ^ - [E=PROTO:http]
RewriteCond %{HTTP_HOST} !^www\. [NC]
RewriteCond %{SERVER_ADDR} !=127.0.0.1
RewriteCond %{SERVER_ADDR} !=::1
RewriteRule ^ %{ENV:PROTO}://www.%{HTTP_HOST}%{REQUEST_URI} [R=301,L]
</IfModule>
Using the same concept you can redirect subdomains as well.
<IfModule mod_rewrite.c>
RewriteCond %{HTTPS} =on
RewriteRule ^(.*)$ - [env=proto:https]
RewriteCond %{HTTPS} !=on
RewriteRule ^(.*)$ - [env=proto:http]
RewriteCond %{HTTP_HOST} ^(www\.)?example\.com$ [NC]
RewriteRule ^ %{ENV:proto}://www.example.com%{REQUEST_URI} [R=301,L]
</IfModule>
.htaccess codes for 301 redirect from www to non-www
To make the 301 redirect from www to non-www (this is important IF your website is NOT using www in the domain portion)
RewriteEngine On
RewriteCond %{HTTP_HOST} www.example.com
RewriteRule (.*) https://example.com/$1 [R=301,L]
#To make 301 redirect from non-www to www
RewriteEngine On
RewriteCond %{HTTP_HOST} !^www\.
RewriteRule ^(.*)$ https://www.%{HTTP_HOST}/$1 [R=301,L]
IMPORTANT You May Need to First Redirect NON-WWW to WWW (or Vice Versa) First
Its very important to triple check Redirection Chain. For example: when someone requests http://example.com what happens? Where is the request redirected to? Understand the fact that www is considered as a sub-domain in terms of Googlebot crawling your website and webpages. Furthermore, asking if your website is installed as a subdomain will also help setup HTTPS protocol working correctly for all URLs.
That means, Search Console Page Experience report for HTTPS Failing with insufficient HTTPS coverage on your website may be incorrect redirection chain for subdomains (www is also considered as a subdomain in DNS). You must serve all subdomains over HTTPS
# Setting Canonical HTTPS/WWW
<IfModule mod_rewrite.c>
Options +FollowSymLinks
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule (.*) https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
#then when NOT www
RewriteCond %{HTTP_HOST} !^www\. [NC]
#redirect to www
RewriteRule (.*) https://www.%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
</IfModule>
# Setting Canonical HTTPS/non-WWW notice the OR operator
<IfModule mod_rewrite.c>
Options +FollowSymLinks
RewriteEngine On
RewriteCond %{HTTPS} off [OR]
RewriteCond %{HTTP_HOST} ^www\.example\.com [NC]
RewriteRule (.*) https://example.com/$1 [L,R=301]
</IfModule>
Shared Hosting Try This
<IfModule mod_rewrite.c>
RewriteCond %{HTTP:X-Forwarded-Port} !443
RewriteRule .* https://%{SERVER_NAME}%{REQUEST_URI} [R=301,L]
</IfModule>
CloudFlare or CDN Try This
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteCond %{HTTP:X-Forwarded-Proto} =http
RewriteRule ^ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
</IfModule>
Or this
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteCond %{HTTP:CF-Visitor} '"scheme":"http"' [OR]
RewriteCond %{HTTPS} !=on
RewriteRule ^(.*)$ - [env=proto:http]
RewriteCond %{HTTP:CF-Visitor} '"scheme":"https"' [OR]
RewriteCond %{HTTPS} =on
RewriteRule ^(.*)$ - [env=proto:https]
</IfModule>
Using Proxy? Try This
# Canonical HTTPS/WWW when behind a proxy
<IfModule mod_rewrite.c>
RewriteCond %{HTTP:X-Forwarded-Proto} =http
RewriteCond %{HTTPS} off
RewriteRule (.*) https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
RewriteCond %{HTTP_HOST} !^www\. [NC]
RewriteRule (.*) https://www.%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
</IfModule>
# Canonical HTTPS/NON-www when behind a proxy
<IfModule mod_rewrite.c>
RewriteCond %{HTTP:X-Forwarded-Proto} =http
RewriteCond %{HTTPS} off
RewriteRule (.*) https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
RewriteCond %{HTTP_HOST} ^www\. [NC]
RewriteRule (.*) https://example.com/$1 [L,R=301]
</IfModule>
RewriteRule .* – [E=HTTP_AUTHORIZATION:%{HTTP:Authorization}] for WordPress CMS .htaccess file
Above .htaccess directives will certainly solve Insufficient HTTPS Coverage on Your Site on various Content Management Systems built on Apache, and yet, if you are using WordPress, you may try adding additional directive HTTP_AUTHORIZATION ensuring correctly serving https for WordPress specific files and directories. Simply modify the default WordPress Specific directives like so:
# BEGIN WordPress
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteRule .* - [E=HTTP_AUTHORIZATION:%{HTTP:Authorization}]
RewriteBase /
RewriteRule ^index\.php$ - [L]
RewriteCond %{REQUEST_FILENAME} !-f
RewriteCond %{REQUEST_FILENAME} !-d
RewriteRule . /index.php [L]
</IfModule>
# END WordPress
You Should Also Test upgrade-insecure-requests
RewriteEngine On
RewriteCond %{HTTPS} !=on
RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301,NE]
Header always set Content-Security-Policy "upgrade-insecure-requests;"
Send Header Response Code Handling Strict-Transport-Security Google Wants so That HTTPS is NOT Failing
Header set Strict-Transport-Security "max-age=31536000; includeSubDomains; preload"
Send Header Response Code Strict-Transport-Security Example 2
Header always set Strict-Transport-Security "max-age=31536000; includeSubDomains; preload" env=HTTPS
Website Issues That Could Cause HTTPS Failing
Regardless of which Content Management System you are using, its smart SEO practice to check your XML sitemap you’ve submitted to Google Search Console. Then, make sure that the URL patterns should be consistent, as in it uses https://
Make sure you have link Canonical URL. Easiest way to check this is through looking at your web page source code (Press CTL+U on your keyword using Chrome). It looks like this:
<link rel="canonical" href="https://www.rankya.com/google-search-console/insufficient-https-coverage-on-your-site/" />
Check and update internal links (menu links, footer links, image links, CSS background-image links) as well as 301 Redirection settings if you are using plugins, update the links if they are still using http:// none-secure version.
Google Search Console Analysis for Fixing Insufficient https Coverage on Your Site
Today in 2021, Google Search Console recommends using Domain Property. This helps Google considerate ALL URLs it knows about websites. If you are still using the URL-prefix property you can leave that in place but start using the new Domain Property option. This will better assist Google understanding URL structure of your entire website (especially if you have 10000s of URLs including subdomains or different language settings on subdomains).
As shows in the above how to video for fixing insufficient HTTPS coverage on your site tutorial, you can use Performance Tab > Create New Filter for Pages > Select URLs Containing http:// HTTPS Status
The above points will most certainly fix HTTPS failing errors for almost all different website setups.
What is Port 80?
Port 80 is the port number assigned to commonly used internet communication protocol (Hypertext Transfer Protocol (HTTP)). Port 80 is used by a computer to send and receive communications from a Web Server. In our case, we are using it for trying to fix Google Webmaster Tools HTTPS Failing issues, its to make sure that requests made to Port 80 to send and receive HTML pages or data are directed to https of a site.

It was a bit difficult when I first tried to understand. I am now more comfortable after reading and realizing the content. The PDF is really insightful and easy to understand.
Thanks.
Hi. thank you very very good post. Nice!
I’m glad you’ve found it of use, thank you for spreading the word about RankYa
nices information on Insufficient HTTPS Coverage thank you so much Rankya.